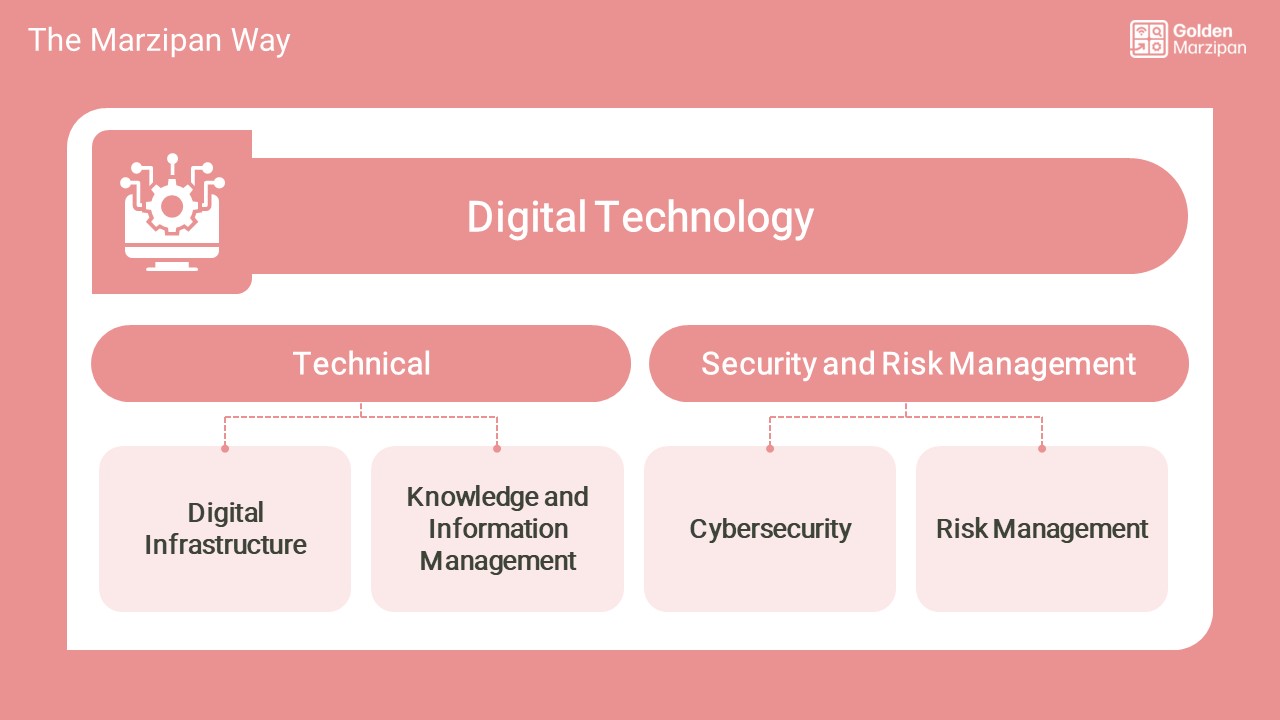
Cyber security | digital technology
Deployment of cybersecurity measures, including strategies for detecting, preventing, and responding to cyber threats.
What does good look like? Our guide to creating digital standards and improving your skills, capacity and capabilities.
Governance
- Clear strategy and policy for cybersecurity, which aligns with its overall digital ICT and business strategy. Cybersecurity measures should comply with relevant laws and regulations, such as GDPR or other data protection laws. This strategy should highlight protection of sensitive resident data.
- Regular audits or assurance measures in place to ensure compliance and identify areas for improvement.
- Organisations are encouraged to apply more specific risk mitigation accreditation through Cyber Essentials Plus or NSCS Cyber Assessment Framework (CAF) or ISO27001.
Prevention and detection
- Robust measures are in place to prevent cyber threats. This could include firewalls, antivirus software, data encryption, secure network protocols, and strong access controls.
- Systems in place for detecting cyber threats. This could include intrusion detection systems, network monitoring, and regular security audits.
- Programme of employee awareness and training in place for threat prevention, such as enforcing strong password practices and educating staff about common cyber threats. Employee training should also address identifying phishing emails and suspicious activity.
Business continuity and recovery
- Incident response plan in place for when a cyber threat is detected. This should include steps for isolating the threat, assessing the damage, restoring systems, and notifying affected parties. There is a comprehensive data backup and recovery plan to ensure data availability in case of an incident. Regular drills or practice scenarios can help ensure that all staff know their roles in the event of a cybersecurity incident.
- Disaster recovery plan for restoring systems and data in the event of a cyberattack or other security incident. This should be part of a larger business continuity plan, which ensures that essential services can continue even in the midst of a cyber incident.
- If the organisation relies on third-party vendors for any of its ICT services, it should ensure that these vendors also have robust cybersecurity measures in place.
- Cyber risk insurance is in place to help an organisation mitigate risk exposure by offsetting costs involved with recovery after a security event. The policies may vary depending on the insurer and the and risks, but typically includes the following: data breach; business interruption; digital asset protection: third-party coverage: network security and privacy liability; reputational harm and media costs.
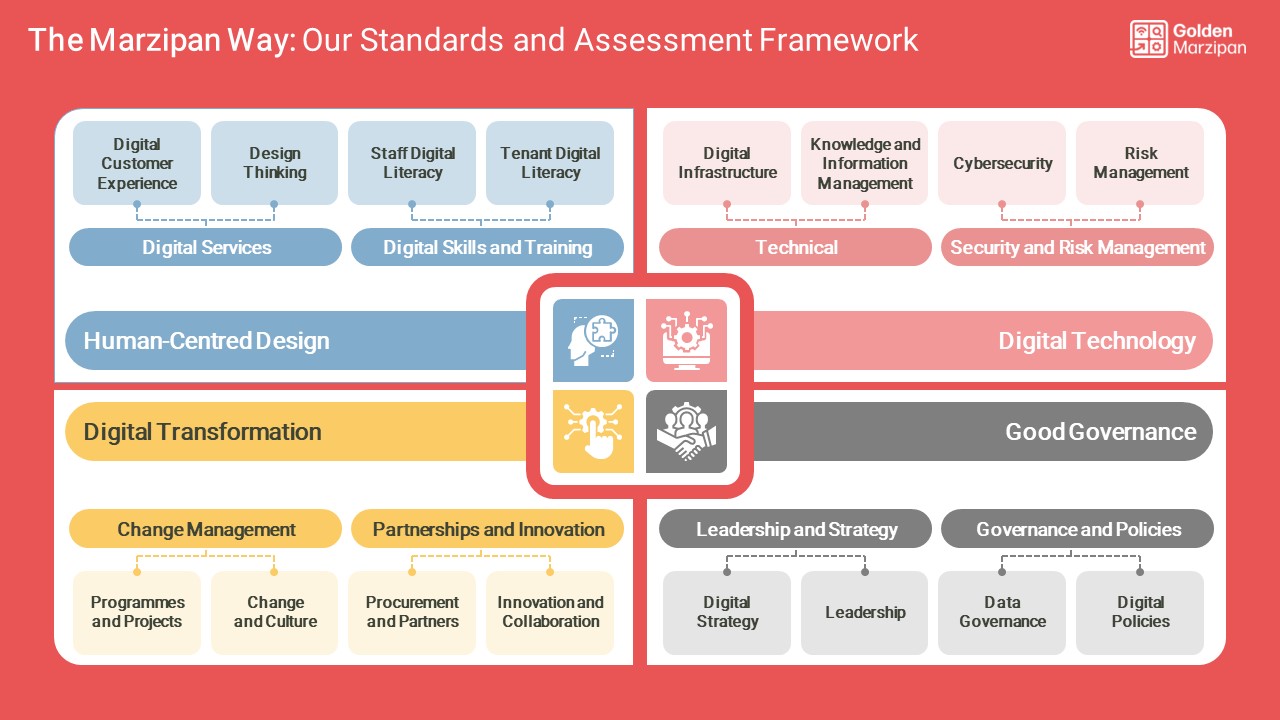
The Marzipan Way is a framework for managing digital transformation in social housing. One page, one section or the whole set of standards, there is something to learn for everyone.
If you would like to learn more, please contact steve@goldenmarzipan.co.uk for a free, no obligation conversation.





